The shift toward containerization has changed the way we build and deploy software forever. However, with this speed comes a new set of risks. Kubernetes is powerful, but out of the box, it is not always secure. As someone who has watched the transition from physical data centers to virtual machines and now to orchestrated containers, I have seen that security is no longer an “afterthought”—it is the foundation. The Certified Kubernetes Security Specialist (CKS) is widely regarded as one of the most challenging and rewarding certifications in the cloud-native ecosystem. It doesn’t just test your ability to run commands; it tests your ability to protect a production environment across the entire build, ship, and run lifecycle.
What is the CKS Certification?
The Certified Kubernetes Security Specialist (CKS) is a performance-based certification exam that validates a professional’s ability to secure container-based applications and Kubernetes platforms during build, deployment, and runtime. It is provided by DevOpsSchool and focuses on best practices for securing the entire container supply chain.
Deep Dive: Certified Kubernetes Security Specialist (CKS)
What it is
The CKS is an advanced, performance-based certification that moves beyond simple cluster management to focus on the defensive posture of your environment. It validates that a professional can secure the entire container lifecycle—from the moment code is written to its execution in a live production cluster. Unlike theoretical exams, it requires you to solve security vulnerabilities in real-time, proving you possess the “battle-tested” skills needed in today’s threat landscape.
Who should take it
This certification is a natural progression for Cloud Engineers, DevOps Professionals, and System Administrators who have already mastered the fundamentals of Kubernetes (CKA). It is also highly recommended for Security Architects transitioning into cloud-native environments who need to understand how traditional security primitives translate to containers. If your goal is to lead high-stakes projects or manage infrastructure that handles sensitive data, this credential is a mandatory requirement.
Skills you’ll gain
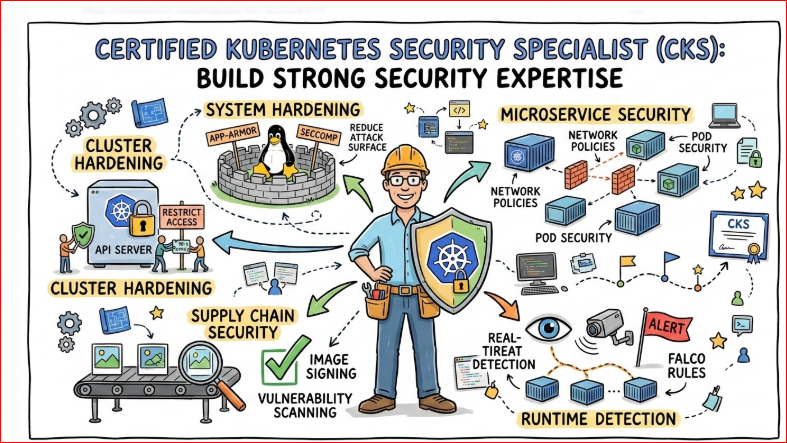
- Cluster & System Hardening: You will learn to minimize the attack surface by securing the API server, disabling insecure defaults, and hardening the underlying host operating system.
- Microservice Isolation: Master the use of Network Policies and specialized security kernels like AppArmor or Seccomp to ensure that a breach in one pod does not compromise the entire cluster.
- Supply Chain Security: Gain the ability to verify image integrity through signing and scanning, ensuring that only trusted, vulnerability-free code reaches your deployment stage.
- Monitoring & Runtime Defense: Develop expertise in detecting behavioral anomalies using tools like Falco and implementing audit logging to maintain a clear trail of all system activities.
Real-world projects you should be able to do
- Zero-Trust Networking: Design and implement a granular network policy architecture that strictly controls traffic flow between microservices, effectively neutralizing lateral movement by attackers.
- Automated Security Gates: Integrate image scanning and policy enforcement (Admission Controllers) into a CI/CD pipeline to automatically block the deployment of non-compliant containers.
- Runtime Threat Detection: Configure and tune real-time monitoring systems to alert on suspicious activity, such as unexpected shell executions or unauthorized file access within a container.
- Compliance Auditing: Perform a comprehensive security audit of an existing Kubernetes cluster to identify misconfigurations and bring it into alignment with global security standards.
Preparation plan
- 7–14 days (The “Fast Track”): This is reserved for experts who are already securing clusters daily. Focus entirely on the exam’s specific command-line environment, practicing the “speed” of your YAML editing and documentation lookup.
- 30 days (The “Professional Path”): Ideal for CKA holders. Dedicate two hours daily to hands-on labs, focusing on the specific third-party tools (like Falco and Trivy) that are unique to the CKS curriculum.
- 60 days (The “Transition Path”): Recommended for those moving from traditional security or sysadmin roles. Spend the first 30 days deeply learning Kubernetes networking and internals before spending the final 30 days on the security-specific modules.
Common mistakes
- Overlooking CKA Basics: Many fail because they lose time on basic troubleshooting. If you cannot quickly fix a broken node or locate a configuration file, you will run out of time for the security tasks.
- Manual Configuration Trap: Trying to memorize every YAML field is a mistake. Instead, practice navigating the official Kubernetes documentation efficiently so you can copy and adapt templates under pressure.
- Ignoring Runtime Security: Candidates often focus too much on “static” security (hardening) and neglect “dynamic” security (runtime). Ensure you spend significant time practicing with Falco rules and audit logging.
- Inefficient Context Switching: The exam involves multiple clusters. Failing to verify which cluster you are currently in before applying a change is a common way to lose points on questions you actually know how to solve.
Choose Your Learning Path
- DevOps Path: Leverage CKS to bridge the gap between development speed and operational safety. This path focuses on automating security so it doesn’t become a bottleneck for your deployment frequency.
- DevSecOps Path: This is the “Security-First” approach where you specialize in building secure pipelines. CKS acts as your primary credential for validating that security is baked into every layer of the infrastructure.
- SRE Path: Use CKS to enhance system reliability. By preventing security incidents—which are essentially a form of catastrophic system failure—you directly contribute to the “Error Budget” and uptime goals of your team.
- AIOps/MLOps Path: As AI workloads scale on Kubernetes, protecting the data and model training environments is critical. CKS provides the necessary foundation to ensure that your ML models and proprietary data remain isolated and secure.
- DataOps Path: Focus on the “Data-at-Rest” and “Data-in-Transit” security primitives within the cluster. This path is for those ensuring that big data pipelines meet strict privacy and regulatory compliance standards.
- FinOps Path: Security breaches, such as unauthorized crypto-mining, are a major source of unexpected cloud costs. CKS empowers you to lock down resources, ensuring your cloud spend is legitimate and optimized.
Best next certification after this
1. Same Track (Specialized Expertise): Certified GitOps Associate (CGOA)
Now that you know how to secure a cluster, the next challenge is managing those security configurations at scale without manual intervention. GitOps is the standard for modern cloud-native operations. This certification proves you can use Git as the “single source of truth” for your security policies, ensuring that your CKS-level hardening is automatically applied and synchronized across hundreds of clusters.
2. Cross-Track (Operational Excellence): FinOps Certified Practitioner
In the current economic climate, “Secure” is only half the battle; your infrastructure must also be “Cost-Efficient.” Security vulnerabilities like crypto-jacking or misconfigured high-availability zones can lead to massive cloud bills. By adding FinOps to your CKS credentials, you position yourself as a “Value Engineer” who can protect the company’s data and its bottom line simultaneously—a rare and highly paid skill set.
3. Leadership Track (Strategic Management): Site Reliability Strategy & Leadership
If you are aiming for a Staff Engineer or Engineering Manager role, you need to move from “doing” to “directing.” This path focuses on building a culture of security and reliability across entire organizations. It teaches you how to manage “Error Budgets,” lead incident response teams, and align technical security goals with business growth, making you an indispensable asset to the C-suite.
Master Certification Table
| Track | Level | Who it’s for | Prerequisites | Skills Covered | Recommended Order |
| Kubernetes | Expert | Security Engineers | CKA Certification | Hardening, Runtime, Supply Chain | After CKA |
| DevOps | Intermediate | DevOps Engineers | Basic Linux/Cloud | CI/CD, Automation, Docker | First |
| SRE | Advanced | SREs | DevOps Foundation | Reliability, Scalability, SLIs | After DevOps |
| FinOps | Intermediate | Managers/Engineers | Cloud Basics | Cloud Billing, Optimization | Any time |
Role → Recommended Certifications
| Target Role | Recommended Certification Path | Primary Focus |
| DevOps Engineer | Docker → CKA → CKS → Jenkins/GitLab | Automating the “Build-Ship-Run” lifecycle securely. |
| SRE | CKA → CKS → Prometheus/Grafana → SRE Professional | Ensuring system reliability through proactive security and monitoring. |
| Platform Engineer | CKA → CKS → Terraform → Service Mesh (Istio) | Building secure, self-service internal infrastructure platforms. |
| Cloud Engineer | Cloud Architect (AWS/GCP/Azure) → CKA → CKS | Managing multi-cloud environments with a “Security-First” mindset. |
| Security Engineer | CKS → DevSecOps Certified Professional → CISSP | Mastering technical container security before moving to high-level strategy. |
| Data Engineer | DataOps Foundation → CKA → CKS | Protecting data pipelines and sensitive information within clusters. |
| FinOps Practitioner | FinOps Certified Practitioner → CKS | Preventing “Resource Leaks” and cost spikes caused by security breaches. |
| Engineering Manager | DevOps Foundation → FinOps → CKS | Understanding technical risks to lead secure and cost-efficient teams. |
Top Institutions for CKS Training and Certification
- DevOpsSchool As a primary leader in the space, DevOpsSchool offers an integrated training program that includes deep-dive technical sessions and official certification support. Their curriculum is designed by industry veterans with decades of experience, focusing on the specific performance-based tasks required to clear the CKS exam on the first attempt.
- Cotocus Cotocus provides a robust platform for cloud-native learning, specializing in “learning by doing.” Their CKS training program is highly rated for its simulated exam environments, which help engineers build the muscle memory needed for cluster hardening and runtime security, backed by a structured path toward official certification.
- Scmgalaxy Known for its extensive community resources and technical workshops, Scmgalaxy offers specialized training tracks for Kubernetes security. They focus on the end-to-end supply chain, providing candidates with the tools and documentation mastery required to manage and secure complex, real-world container environments.
- BestDevOps BestDevOps offers focused bootcamps that prioritize exam readiness alongside practical implementation. Their training packages often include mentored lab sessions and certification guidance, making it an excellent choice for working professionals who need to balance intensive study with their daily operational responsibilities.
- Specialized Domain Schools For those looking to align their CKS certification with a specific career niche, specialized platforms like devsecopsschool.com, sreschool.com, and aiopsschool.com offer tailored versions of the CKS curriculum. These programs ensure that the security principles you learn are directly applicable to your specific role in security, reliability, or artificial intelligence operations.
FAQs about CKS (General)
1. How difficult is the CKS exam?
It is considered one of the toughest in the industry because it is 100% performance-based. You must solve real problems in a live cluster under time pressure.
2. How long does the CKS certification last?
The certification is valid for two years from the date of passing.
3. Is CKA a strict prerequisite?
Yes. You must hold a valid (non-expired) CKA certification to sit for the CKS exam.
4. How much time should I dedicate to studying?
Most working professionals need between 4 to 8 weeks of consistent study (10-15 hours per week) to feel confident.
5. What is the format of the exam?
It is a proctored, online, performance-based test. There are no multiple-choice questions; only tasks to perform on the command line.
6. Does the CKS help with salary growth?
Absolutely. Kubernetes security is a niche skill. Professionals with a CKS often command 20-30% higher salaries than those with just general DevOps skills.
7. Can I use the official Kubernetes documentation during the test?
Yes, you are permitted to have one extra tab open with official documentation (Kubernetes.io, GitHub/Falco, etc.).
8. What happens if I fail the first time?
Most providers, including DevOpsSchool, offer a free retake if you don’t pass on your first attempt.
9. Is CKS relevant for AWS EKS or Google GKE?
Yes. While the exam uses a standard cluster, the principles of hardening, network policies, and runtime security apply to all managed Kubernetes services.
10. Do I need to be a developer to pass CKS?
No, but you should be comfortable with YAML and basic shell scripting.
11. Is the exam proctored?
Yes, it is remotely proctored via webcam and screen sharing.
12. Why should I choose CKS over other security certifications?
Unlike theoretical exams, CKS proves you can actually secure a live system. It is highly respected by hiring managers for this reason.
FAQs Specific to the CKS Certification
1. What is the passing score for CKS?
The passing score is typically around 67%, though this can vary slightly based on the exam version.
2. What version of Kubernetes does the exam use?
The exam usually tracks the most recent stable versions. It’s important to practice on the version specified in the curriculum.
3. How do I access the exam environment?
You access it via a terminal in your web browser. No local installation of Kubernetes is required for the test itself.
4. Are third-party tools like Falco or Trivy included?
Yes, the CKS curriculum includes specific third-party security tools that are standard in the industry.
5. Can I skip questions and come back later?
Yes, you can move between questions. It is often a good strategy to tackle the easy tasks first.
6. Is there a specific Linux distribution used?
The exam environment is typically based on Ubuntu.
7. How quickly do I get my results?
Results are usually emailed within 24 to 36 hours after completing the exam.
8. Is CKS worth it if I already have a security degree?
Yes. Academic degrees often lack the hands-on “in-the-trenches” skill validation that the CKS provides.
Testimonials
“I had been working with Kubernetes for three years, but the CKS training opened my eyes to vulnerabilities I didn’t even know existed. It changed how I architect systems.” – Arjun V.
“The hands-on nature of this certification is what makes it valuable. When I show my CKS badge, recruiters know I can actually do the work, not just talk about it.” – Sarah L.
“Coming from a traditional security background, CKS was the bridge I needed to become relevant in the world of cloud-native applications.” – Rohan M.
Next Certifications to Take
Once you have mastered the CKS, where should you go next? I recommend these three directions:
- Same Track (Expertise): Certified GitOps Associate (CGOA) to learn how to manage these security configurations as code.
- Cross-Track (Broadening): FinOps Certified Practitioner. Now that you’ve secured the cluster, learn how to make it cost-effective.
- Leadership (Management): Engineering Management or Site Reliability Strategy programs to lead larger teams in implementing these security cultures.
Conclusion
Securing a Kubernetes cluster is a journey, not a destination. The Certified Kubernetes Security Specialist (CKS) is the gold standard for proving you have the skills to protect modern workloads. Whether you are an engineer looking to level up or a manager looking to secure your organization’s future, this path is one of the most impactful investments you can make in your career today.